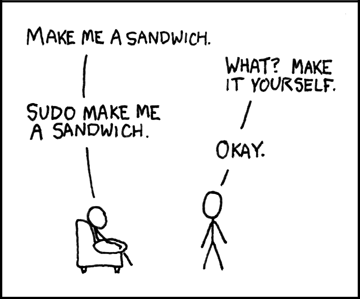
 Sudo
Sudo
Q: How come "which ifconfig" (runing as a user)Â finds nothing, yet "sudo ifconfig" does work?
A: sudo has a compile-time parameter called with-secure-path, which sets a different PATH for the sudo environment. Debuntu secure path contains /sbin:/usr/sbin, and that's how it works. This feature gets two goals: convenience (no full path required for common root cmds) and security (ignoring potentially bad user PATH).
NOTE that RHEL doesn't use this option, and running "sudo ifconfig" there simply fails.
Q: How come sudo requests a password only on the first run?
A: Sudo has a nice mechanism for creating these "sudo session" things. After authentication, sudo creates a 'timestamp dir' (in /var/run/sudo on my Debian), then uses its date to check when the last successful authentication took place.
- Session timeout is configurable, defaults to 15mins.
- sudo -k kills this session by simply removing the timestamp dir.
All info is found in the sudo(8) and sudoers(5) manpages
Setuid and LD_LIBRARY_PATH
Just a quick insight from my workplace: to my surprise, a setuid binary deliberately ignores many environment variables such as LD_LIBRARY_PATH and LD_PRELOAD.
Security Shmecurity..